Cybersecurity Solutions Every Modern Business Needs
Today businesses rely on cloud services and SaaS applications, but this can be risky if they don’t have security solutions to secure such environments. Today’s decentralized work situations, where many employees work remotely, also create more security risks. As threats escalate, cybersecurity solutions evolve. Businesses can no longer rely on simple solutions such as an antivirus or a firewall. Here are some of the cybersecurity solutions modern businesses need today.
Table of Contents
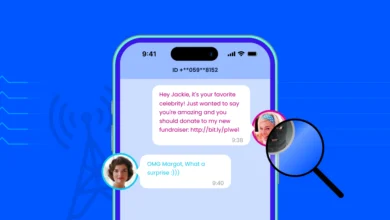
Advanced email security solutions
Next-generation email security software is necessary to prevent phishing, impersonation, BEC attacks, malware etc. Advanced email protection software deployed in the cloud or on-premise can detect and block malicious emails using AI to evaluate behavior patterns and detect irregularities. These methods of email protection provide a way to prevent employees from clicking on phishing emails and exposing businesses to threats.
Identity and access management (IAM) tools
Today businesses can’t just give unlimited access to employees within a corporate network perimeter. They need to secure identities and limit access to mitigate risks. They will use IAM services managed by providers in the cloud.
- Identity authentication: IAM solutions help companies to develop authentication policies and set privileges for different users. They authenticate credentials for users against a database.
- Access management: Solutions use identity information to determine the extent of access users can have.
- Zero-trust policies: In the past, businesses had the policy that if employees were into a system, they had access, and that was that. Zero-trust policies today mean all employees are constantly identified and have their access managed.
Remote Access VPNs
With a VPN, businesses can require users to present login credentials, and it encrypts all the data exchanged. With end-to-end encryption, all data transfers are unreadable to unauthorized actors. VPNs can therefore shield corporate assets and protect network security.
Multifactor authentication and password management solutions
For a business solely dependent on VPNs, it’s important to integrate multi factor authentication tools for an extra security layer. Multifactor authentication requires multiple means of identification to get access. Implementing multi factor authentication for customers gives a clear indication that businesses care about their security. Customers are more trusting and comfortable when they know that businesses are trying to protect them.
Automated password management solutions can also ensure that employees stay up-to-date with strong passwords.
Endpoint Detection and Response (EDR)
Modern businesses need to find ways to ensure that all the laptops, desktops, and mobile devices connected to their network are secure, especially now that many employees are working remotely.
- EDR solutions make it easy to:
- Detect devices connected to a network
- Get details about cybercriminal activities
- Respond to threats the system recognizes
- Collect forensic information in the event of a breach
MDR solutions are an endpoint protection service to detect, prevent, and respond to attacks across many vectors. As opposed to searching for malware characteristics, MDR solutions monitor the processes of endpoints and recognize deviations from the norm.
Edge computing solutions
Where endpoint protection covers individual devices, edge security supports all of the devices together at the point where they go between a business environment and the public internet. Using edge security solutions means employees can work from anywhere on any device without compromising the safety of systems or sensitive data.
Advanced antivirus software
Traditional antivirus software was good at catching computer viruses, but modern versions can defend against other threats too. Robust antivirus software can help to catch malware attacks by checking for evidence of any known threats. It uses existing attack profiles that have affected users to identify threats so they can be eliminated. Highly advanced antivirus software can guard against Trojan attacks, ransomware, spyware, keyloggers and spyware.
Next-generation firewalls
Next-generation firewalls (NGFW) offer protection against a range of threats. They inspect data packets going to and from the network. If they detect a known threat, they will discard the data package. They also use machine learning to detect malicious behavior and can even stop zero-day attacks.
Unified Threat Management (UTM) devices provide:
- Next-gen firewalls
- Antivirus and anti-malware
- Intrusion prevention
Domain name system (DNS) protection
This type of protection provides an additional security layer as it prevents employees from accessing malicious websites. They can also filter out content you prefer users not to access, or you don’t want infiltrating your network. If an employee is used to accessing a website with known threats in their private time, they may also try to do so while at work. Your DNS protection service will prevent them from connecting to the site while on your network.
Security information event management (SIEM) system
This is a monitoring solution companies can integrate with major tech providers such as Microsoft. It alerts businesses if it recognizes a suspicious login or sees many failed login attempts. It can spot general instances of abnormal behavior and basically create a centralized database of threats to escalate them to an IT team for them to mediate in real time.
Comprehensive cybersecurity solutions
There are various cybersecurity solutions that offer a variety of services. This may include incident response, vendor risk management, and disaster recovery. Using such solutions can help small businesses to build out a comprehensive cybersecurity policy. In many cases, partnering with IT consulting services can help organizations align these solutions with long-term business and security goals.
A cybersecurity training program is essential for any modern business to make sure employees are fully aware of threats they may encounter and how to exercise best cybersecurity practices. Regular and extensive training can change their cybersecurity habits.
Conclusion
Increasingly sophisticated cyber criminals and emerging technologies like IoT and edge have created a much broader attack surface. This has increased the complexities of security. Modern businesses need to have ways to keep their business data, cash flow and their customers safe online. Even if businesses can’t protect themselves entirely against all the threats, the above cybersecurity solutions can help them to reduce the risks.